Using the default boot.img provided on the other thread, I’ve generated a Magisk 21.4 boot.img. I’m not sure if I’m allowed to post the binary here, but here’s some instructions on how I did it. These may not work for you, as these are Linux only.
--LINUX--
This could break your device and I'd like to not be responsible. Please exercise caution when flashing to your device. If you don't know what you are doing please wait :)
Get Magisk Manager on device, put default 2e boot.img on the device, use Magisk to make patched boot.img. Pull back using adb.
adb pull /sdcard/Download/magisk_patched_q4VX5.img
Split
split -b 16M magisk_patched_q4VX5.img
rm magisk_patched_q4VX5.img xab
mv xaa magisk_patched_q4VX5.img
Generate signing keys
openssl genrsa -out rsa.pem 2048
Install avbtool and use
./avbtool.py add_hash_footer --image "magisk_patched_q4VX5.img" --partition_size 33554432 --partition_name boot --key rsa.pem --prop com.android.build.boot.os_version:10 --prop com.android.build.boot.security_patch:2019-06-06 --algorithm SHA256_RSA2048
Boot into bootloader
adb reboot bootloader
Flash image
fastboot flash boot magisk_patched_q4VX5.img
Reboot back into regular
fastboot reboot
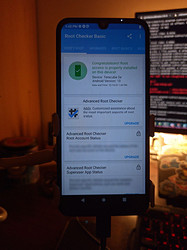
Everything should work.
some more info and sources:
https://github.com/topjohnwu/Magisk/issues/2491#issuecomment-773928239
https://android.googlesource.com/platform/external/avb/+/master/README.md
https://wiki.postmarketos.org/wiki/Android_Verified_Boot_(AVB)
 .
.


 !
!